Next week brings with it the ALA Midwinter 2016 meeting, which means I’m bundling myself up and heading back to Boston for a few days to revel in more library than anyone can take. This is my first ALA conference in almost a decade in which I don’t have overwhelming amounts of LITA commitments (the last ten years looked like: Created an interest group > Chaired said Interest Group > Chaired committee > Elected as Director-at-Large to Board > Appointed as committee chair and Parliamentarian of board). So what did I do with all of my newfound freedom and time?
Over-scheduled myself like mad, of course.
Here’s a quick rundown of things I’m getting myself into at ALA Midwinter! If you’d like to meet with me about anything, I would love to talk to you. Drop me an email and let’s find some time to meet up!
Booth 2232
For the first time, the Measure the Future Project will have a booth in the ALA Midwinter Exhibit Hall! We will be showing off examples of what we’re building, including hardware and software, and will be taking signups for libraries and librarians interested in the project. I’ll be at the booth any time I’m not speaking at one of the below, so if you’re looking for me, it’s a good bet that’s where I’ll be. We’ll have cool giveaways, a LibraryBox sharing information about the project, and we’re sharing a booth with the Library Freedom Project (who are basically made of cool and awesome and you know you want to come hang out).
Thursday
7-10pm
EMW Drink Salon on Tech & Ethics: Libraries
EMW Bookstore, 934 Massachusetts Ave, Cambridge, MA
https://emwdrinksalon-libraries.splashthat.com/
This is going to be an amazing time. Trust me. Take a look at the website, register, come have some drinks and talk tech and ethics with a bunch of awesome people.
Saturday
Knight News Challenge on Libraries 2016
9-10am, Convention Center Room 206A/B
Myself and a few other of the winners of the previous Knight News Challenge for Libraries will be on a panel with Knight Foundation staff to discuss how you (YES YOU) can apply for a News Challenge grant. Open to individuals as well as organizations, this is IMNSHO the very best funding available for library projects. If you have any ideas that you’ve been kicking around, now is the time to pick them up and dust them off and polish them up. Another News Challenge is coming this year, and if you want to know how to apply from previous grantees….this is the way to do it.
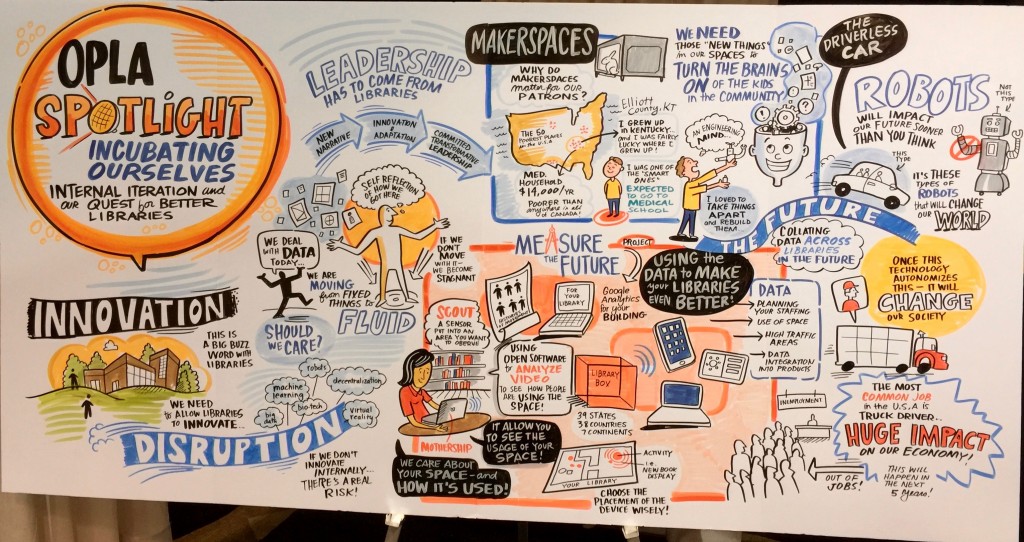
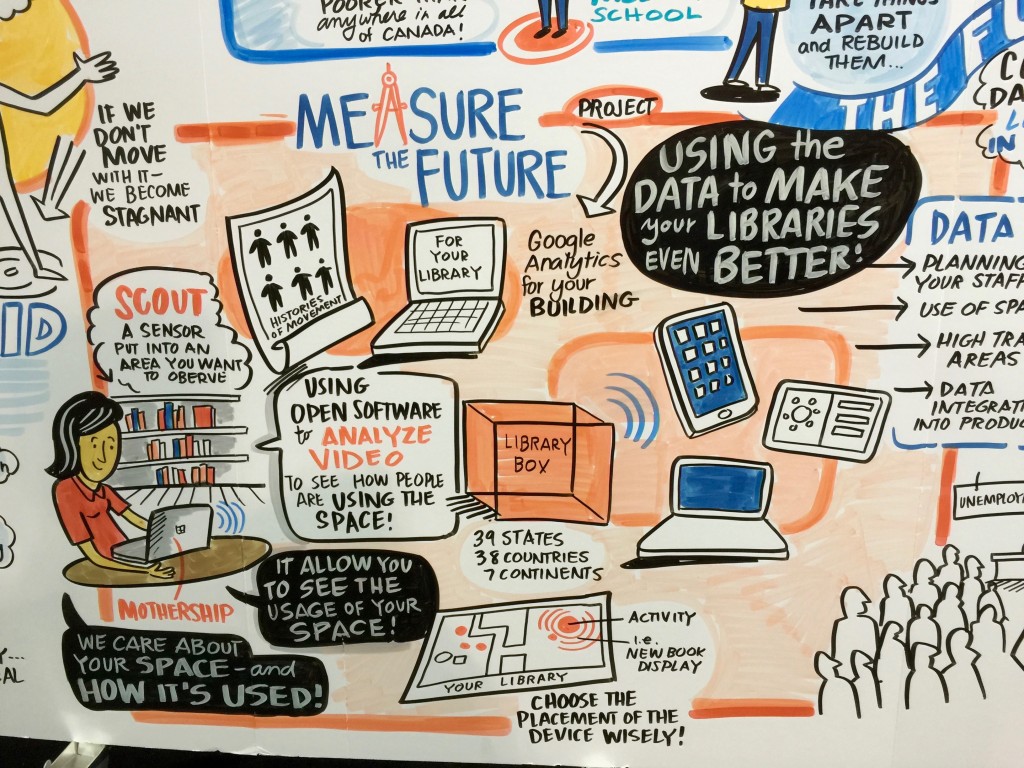
Master Series: Measuring the Future
12:30pm-1:30pm, Convention Center Room 206A/B
One of the most valuable assets a library has is the physical building itself, but aside from gate count we have remarkably little information about how it’s used. What if you could have a Google Analytics style dashboard and understanding of what happened in your library yesterday? Over time, longitudinal data about activity in your library can do amazing things: allow you to plan staffing predictively, let you A/B test displays or furniture arrangements, check what rooms are most popular during different parts of the day or year, and much more. Why just collect statistics when you can use them to actively make your library better for both staff and patrons? Come have a discussion with us about these issues and let us know what you’d like to see from the Measure the Future project!
Sunday
LITA Top Technology Trends
10:30-11:30am, Convention Center Room 253A
I’ve been lucky enough to be a part of this august panel a handful of times in the past, and I’m thrilled to be included again. This time around I will be talking about Blockchain and its potential to revolutionize library systems, with a detour over into the Rise of the Machines (AI, computer vision, semantic analysis, ubiquitous computing, mesh networks, Internet of Things) and how that is going to make the future stranger than we can imagine. This is a do-not-miss panel (not because of me, but…trust me).
LITA Happy Hour
6:00-8:00pm, MIJA Cantina & Tequila Bar, Quincy Market, 1 Faneuil Hall Marketplace
The best gathering of library technologists anywhere, LITA Happy Hour is an amazing time full of awesome people. This is the best place to meet tons of techie librarians, and is where I will be happily sipping a drink amongst friends. Come introduce yourself and say hello if you make it!
This doesn’t count the half-dozen other non-public meetings I’m attending, or seeing friends and such. It’s gonna be fun, and exhausting, and great. Come see me at the booth! I look forward to meeting all the librarians I don’t know yet, and can’t wait to see old friends.